Metasploit Wrap-Up 12/8/2023

Are You Looking for ACTION?

Our very own adfoster-r7 has added a new feature that adds module actions, targets, and aliases to the search feature in Metasploit Framework. As we continue to add modules with diverse goals or targets, we’ve found ourselves leaning on these flags more and more recently, and this change will help users better locate the modules that let them do what they want.
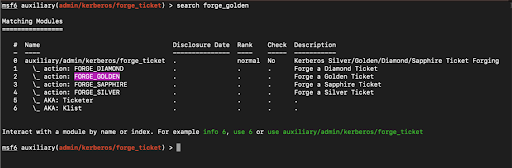
Right now, the feature is behind a feature flag as we work out how to make it as user-friendly as possible. If you would like to use it, turn on the feature by running features set hierarchical_search_table true. Please let us know how it works for you!
New module content (2)
ownCloud Phpinfo Reader
Authors: Christian Fischer, Ron Bowes, creacitysec, h00die, and random-robbie
Type: Auxiliary
Pull request: #18591 contributed by h00die
Path: gather/owncloud_phpinfo_reader
Description: This adds an auxiliary module for CVE-2023-49103 which can extract sensitive environment variables from ownCloud targets including ownCloud, DB, Redis, SMTP, and S3 credentials.
Docker cgroups Container Escape
Authors: Kevin Wang, T1erno, Yiqi Sun, and h00die
Type: Exploit
Pull request: #18578 contributed by h00die
Path: linux/local/docker_cgroup_escape
Description: This adds a new module to exploit CVE-2022-0492, a docker escape for root on the host OS.
Enhancements and features (5)
- #17667 from h00die - Makes various performance and output readability improvements to Metasploit's password cracking functionality. Now, hash types without a corresponding hash are skipped, invalid hashes are no longer output, cracking stops for a hash type when there’s no hashes left, and empty tables are no longer printed. Other code optimizations include added support for Hashcat username functionality, a new quiet option, and documentation updates to the wiki.
- #18446 from zeroSteiner - This makes the DomainControllerRhost option optional, even when the authentication mode is set to Kerberos. It does so by looking up the Kerberos server using the SRV records that Active Directory publishes by default for the specified realm.
- #18463 from h00die-gr3y - This updates the
linux/upnp/dlink_upnp_msearch_execexploit module to be more generic and adds an advanced detection logic (checkmethod). The module leverages a command injection vulnerability that exists in multiple D-Link network products, allowing an attacker to inject arbitrary command to theUPnPvia a crafted M-SEARCH packet. This also deprecates themodules/exploits/linux/upnp/dlink_dir859_exec_ssdpcgimodule, which uses the same attack vector and can be replaced by this updated module. - #18570 from adfoster-r7 - Updates Metasploit's Docker ruby version from 3.0.x to 3.1.x.
- #18581 from adfoster-r7 - Adds hierarchical search table support to Metasploit's search command functionality. The search table now includes a module's actions, targets, and alias metadata. This functionality requires the user to opt-in with the command
features set hierarchical_search_table true.
Bugs fixed (1)
- #18603 from h00die - Updates the
auxiliary/scanner/snmp/snmp_enumandauxiliary/scanner/snmp/snmp_loginmodule metadata to include metadata references to CVE-1999-0516 (guessable SNMP community string) and CVE-1999-0517 (default/null/missing SNMP community string).
Documentation added (1)
You can always find more documentation on our docsite at docs.metasploit.com.
Get it
As always, you can update to the latest Metasploit Framework with msfupdate and you can get more details on the changes since the last blog post from GitHub:
If you are a git user, you can clone the Metasploit Framework repo (master branch) for the latest.
To install fresh without using git, you can use the open-source-only Nightly Installers or the
commercial edition Metasploit Pro