IR Trends: Ransomware on the rise, while technology becomes most targeted sector


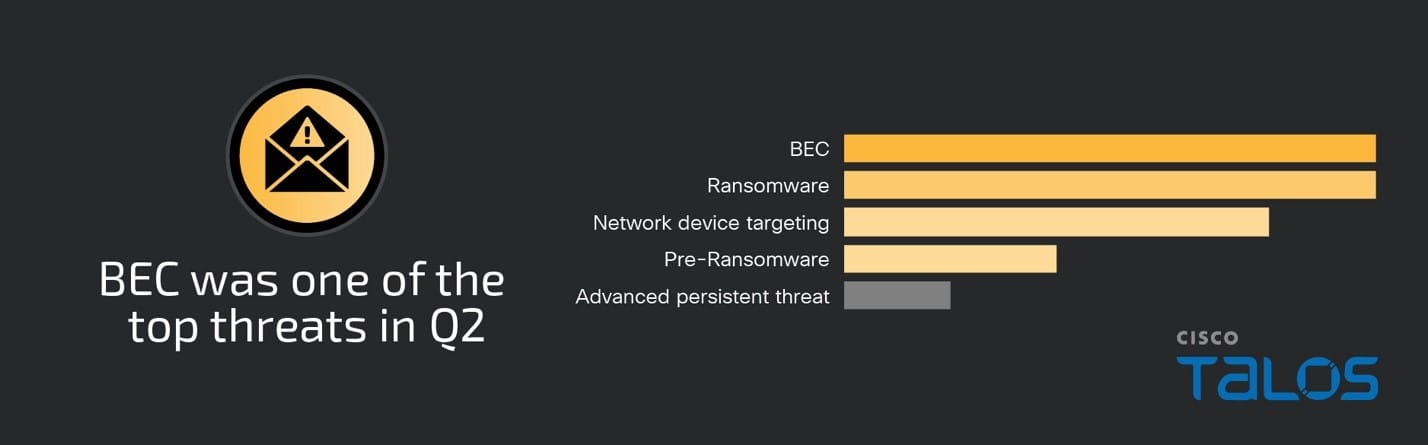
Business email compromise (BEC) and ransomware were the top threats observed by Cisco Talos Incident Response (Talos IR) in the second quarter of 2024, together accounting for 60 percent of engagements.
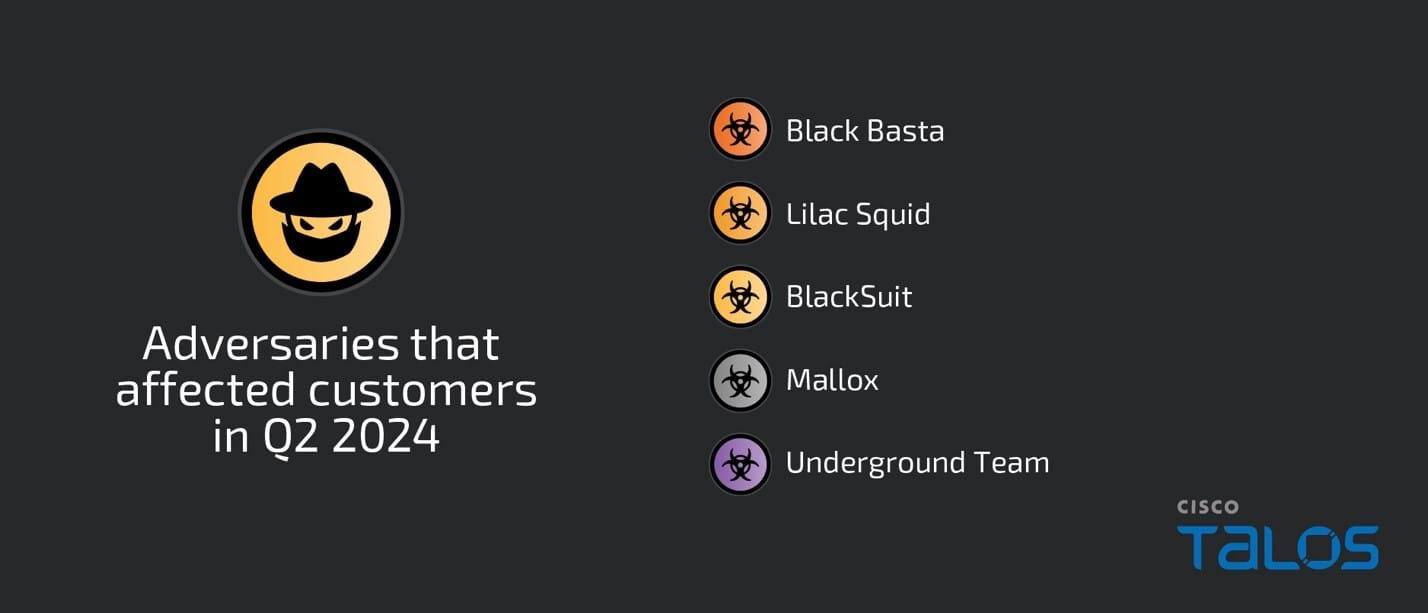
Although there was a decrease in BEC engagements from last quarter, it was still a major threat for the second quarter in a row. There was a slight increase in ransomware where Talos IR responded to Mallox and Underground Team ransomware for the first time this quarter, as well as the previously seen Black Basta and BlackSuit ransomware operations.
For the third quarter in a row, the most observed means of gaining initial access was the use of compromised credentials on valid accounts, which accounted for 60 percent of engagements this quarter, a 25 percent increase from the previous quarter.
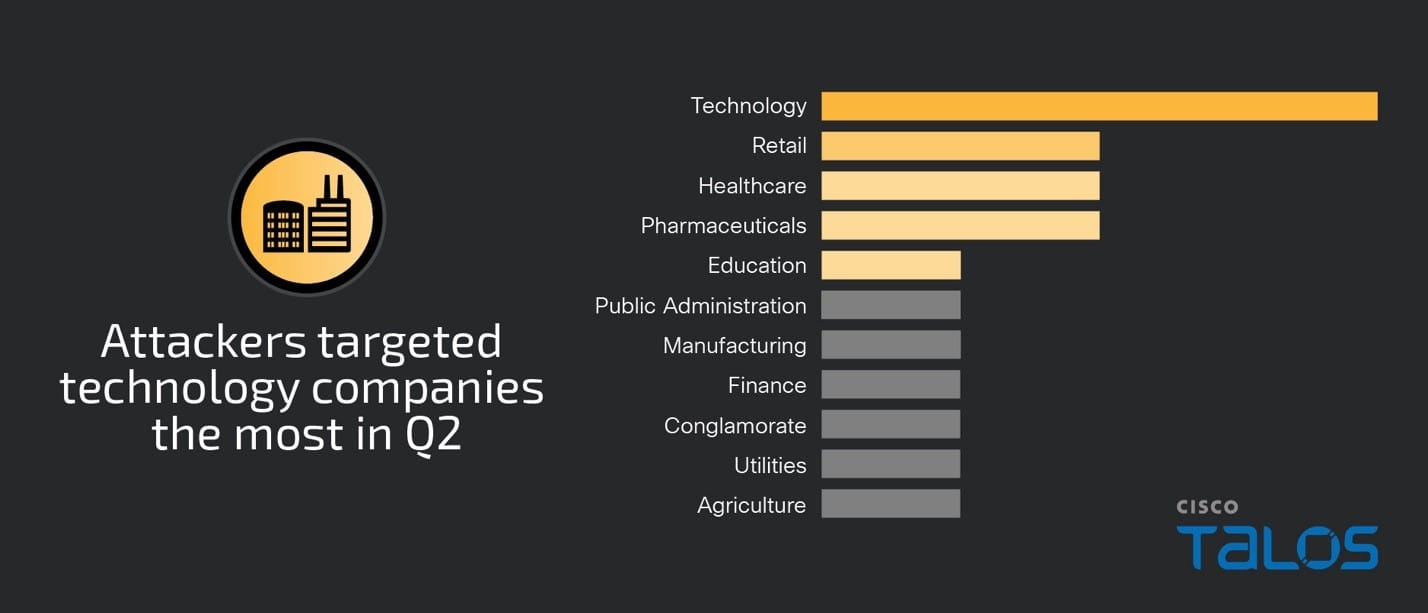
Technology was the most targeted vertical this quarter, accounting for 24 percent of engagements, closely followed by healthcare, pharmaceuticals and retail. There was a 30 percent increase in engagements affecting the technology sector from the previous quarter. Organizations in the technology sector may be seen as gateways into other industries and organizations given their significant role in supplying and servicing a wide range of sectors, making them attractive targets for adversaries.
Technology organizations often have extensive digital assets supporting critical infrastructure, which means they have minimal tolerance for downtime and may, therefore, be more likely to pay extortion demands.
Talos IR also observed a slight increase in network device targeting this quarter, accounting for 24 percent of engagements. This activity included password-spraying, vulnerability scanning and exploitation.
Watch discussion on the report's biggest trends
Surge in BEC continues
Within BEC attacks, adversaries will compromise legitimate business email accounts and use them to send phishing emails to obtain sensitive information, such as account credentials. Adversaries can also use compromised accounts to send emails with fraudulent financial requests, such as changing bank account information related to payroll or vendor invoices.
In a few of the observed BEC incidents that involved a method of phishing as an infection vector, adversaries leveraged SMS phishing, or “smishing,” to compromise accounts. This involves adversaries sending fraudulent text messages to trick recipients into sharing personal information or clicking on malicious links.
Targeting employees’ personal mobile devices can be an effective method for initial access because they may not have the same security controls as their corporate devices. Organizations should ensure SMS phishing scams are included in security awareness training for employees.
In one engagement, adversaries compromised a user’s account by sending a phishing email to the employee’s personal email address that redirected the user to a fake login page. The user had passwordless authentication through an authenticator application but received a multi-factor authentication (MFA) push notification and accepted it, granting the adversary access.
In another cluster of activity, adversaries used compromised credentials obtained through unknown means to access a valid email account. The adversary then created Microsoft Outlook mailbox rules to send emails to a folder named “deleted” before using the compromised account to send out over a thousand phishing emails to internal and external recipients. The phishing emails contained a link that led to a fake login page intended to harvest credentials.
Ransomware trends
Ransomware accounted for 30 percent of engagements this quarter, a 22 percent increase from the previous quarter. Talos IR observed Mallox and Underground Team ransomware families for the first time this quarter. Talos IR also responded to the previously seen Black Basta and BlackSuit ransomware this quarter, which we recently assessed are two of the top players within the current ransomware landscape.
Notably, 80 percent of ransomware engagements this quarter lacked proper MFA implementation on critical systems, such as virtual private networks (VPNs), playing a role in allowing adversaries to gain initial access. In addition, command obfuscation, such as Base64 encoding, was observed within 40 percent of ransomware engagements this quarter, likely to evade detection by disguising the true intent of the commands.
Mallox
In a Mallox ransomware engagement, adversaries compromised and encrypted a single Microsoft SQL server, consistent with public reporting on Mallox ransomware attacks. There were no signs of data staging, exfiltration or lateral movement. Talos IR could not determine the initial access vector due to a lack of customer telemetry.
First discovered in 2021, Mallox (also known as TargetCompany and Fargo) is a ransomware-as-a-service (RaaS) operation that leverages double extortion techniques. Mallox has Linux and Windows variants of the encryptor and appends the file extension “.malox” to files after encryption. The operation is known to use brute force techniques to target unsecured Microsoft SQL servers and has been observed using Cobalt Strike beacons during attacks, although Talos IR did not observe Cobalt Strike in this incident. Cobalt Strike is a legitimate penetration testing tool that is commonly leveraged by adversaries for malicious activity.
Underground Team
Talos IR responded to an Underground Team ransomware attack in an engagement where the adversary leveraged Secure Shell (SSH) to move laterally in the environment. The adversary also strategically reactivated certain Active Directory user accounts that had been previously disabled, potentially a newly observed technique for Underground Team ransomware operators, based on a lack of public reporting.
Talos IR’s review of the available Active Directory logs indicated that the adversary reactivated over 100 previously disabled accounts, likely an attempt to escalate privileges. Talos IR reviewed a specific compromised account leveraged by the adversary to establish persistence and move laterally. Using this account, the adversary also deployed the ransomware payload and encrypted multiple critical systems, including domain controllers, virtual machines, backups and server management systems.
During the engagement, the threat actor also sent harassing messages to employees' personal emails. This technique was likely intended to coerce the victim to respond to the actor’s demands.
Underground Team is a relatively new ransomware group that emerged in 2023. While not as prominent as other established ransomware actors, they have garnered attention for their tactics, techniques and procedures (TTPs) and how the group claims to offer cybersecurity help within their extortion demands, a common social engineering technique.
BlackSuit
Talos IR responded to a BlackSuit ransomware attack where adversaries gained access with valid credentials through a VPN that was not protected by MFA. Persistence was established by deploying the remote management tool AnyDesk in the environment, as well as Cobalt Strike. There is no easy way to effectively block all unauthorized remote management tools, but security can be greatly improved through a combination of policy and technical controls.
Talos IR also observed the adversaries deploying several utilities not previously observed being leveraged by BlackSuit. The group used Microsoft PowerToys for lateral movement, SuperGrate, a Windows User Profile backup and migration utility, and Mimikatz DCSync, an old technique commonly leveraged by other ransomware operations to compromise credentials.
The adversaries also leveraged living-off-the-land binaries (LoLBins) like PsExec and the Windows Management Instrumentation command-line (WMIC) to move laterally across the network. Several legitimate tools were installed to assist with staging and exfiltrating data, such as WinRAR and WinSCP, commonly used by ransomware operations. The files delivering the ransom notes could also not be easily analyzed due to sandbox evasion techniques, a technique not typically observed within BlackSuit attacks.
BlackSuit is a RaaS group that has been active since at least May 2023, gaining notoriety after the group’s threat to entities in the healthcare sector in November 2023. BlackSuit’s ransomware encryptors, supporting Linux and Windows variants, have been observed to have many similarities with the Royal ransomware group, leading researchers to believe BlackSuit is a rebrand of Royal ransomware operations. Talos and other researchers have compared the Royal and BlackSuit encryptors and confirmed the code was extremely similar.
Black Basta
Talos IR responded to a Black Basta engagement this quarter where adversaries gained initial access using compromised credentials on a valid RDP account that was not protected with MFA. Once inside the network, adversaries began acquiring credentials from the Windows Credential Manager through the New Technology LAN Manager (NTLM). Talos IR observed the adversaries using remote PowerShell execution, which is a common technique that uses WinRM to start a shell on remote systems.
The adversaries leveraged the open-source command line tool Rclone to facilitate data exfiltration, a technique commonly used by ransomware actors. The Rclone configuration file was deleted before the adversary finished their attack. Sometimes, adversaries will forget to delete the configuration file, providing defenders with access tokens for the adversary-controlled server where the data was exfiltrated.
This can allow defenders to download the stolen files and then delete them from the servers. Remote services, including RDP and SMB, were leveraged for lateral movement. Before the execution of ransomware, the adversaries disabled several tools, such as Windows Defender, to ensure the encryption process would not be interrupted.
First discovered in April 2022, Black Basta is a RaaS operation that is a likely rebrand of the former Conti ransomware group that was shut down in Spring 2022. Black Basta ransomware is written in C++ and targets Windows and Linux systems. Black Basta affiliates have been observed using a wide range of initial access techniques, such as phishing, drive-by compromise, password spraying and exploiting known vulnerabilities. The targeting appears to be opportunistic and/or indiscriminate in nature.
Network device targeting
Talos IR observed a slight increase in network device targeting this quarter, accounting for 24 percent of engagements. This activity included password spraying, vulnerability scanning and exploitation. Network devices should be regularly patched and actively monitored because they provide a critical path for data entering and leaving the network. If compromised, an adversary could immediately pivot into an organization, divert or change network traffic, and monitor network communications.
In one engagement, adversaries exploited a denial-of-service (DoS) vulnerability, tracked as CVE-2018-0296, affecting a Cisco Adaptive Security Appliance (ASA). The vulnerability in the web interface could allow an unauthenticated, remote attacker to cause a targeted device to reload unexpectedly, resulting in denial–of service.
Adversaries also exploited a separate vulnerability within the Cisco ASA, tracked as CVE-2020-3259, that allowed them to remotely retrieve memory contents on the ASA, resulting in the unauthorized disclosure of sensitive information. Both the hardware and software used by the organization were past end-of-life (EOL) support. Talos IR recommends using supported hardware and software to prevent unwanted downtime and cyberattacks.
In another cluster of activity, adversaries carried out a series of password-spraying attacks against the clientless VPN functionality of the organization’s ASA firewalls. The clientless functionality allows users to have a secure, remote access VPN tunnel to an ASA using a web browser without requiring a software or hardware client.
The attack was ultimately unsuccessful because the organization enforced certificate-based authentication, which uses digital certificates stored in the user’s browser. If a user attempted to authenticate without a certificate, they would not be granted access.
Initial vectors
When known, the most observed means of gaining initial access was the use of compromised credentials on valid accounts, which accounted for 60 percent of engagements There was a 25 percent increase from the previous quarter where valid accounts were also a top attack vector.
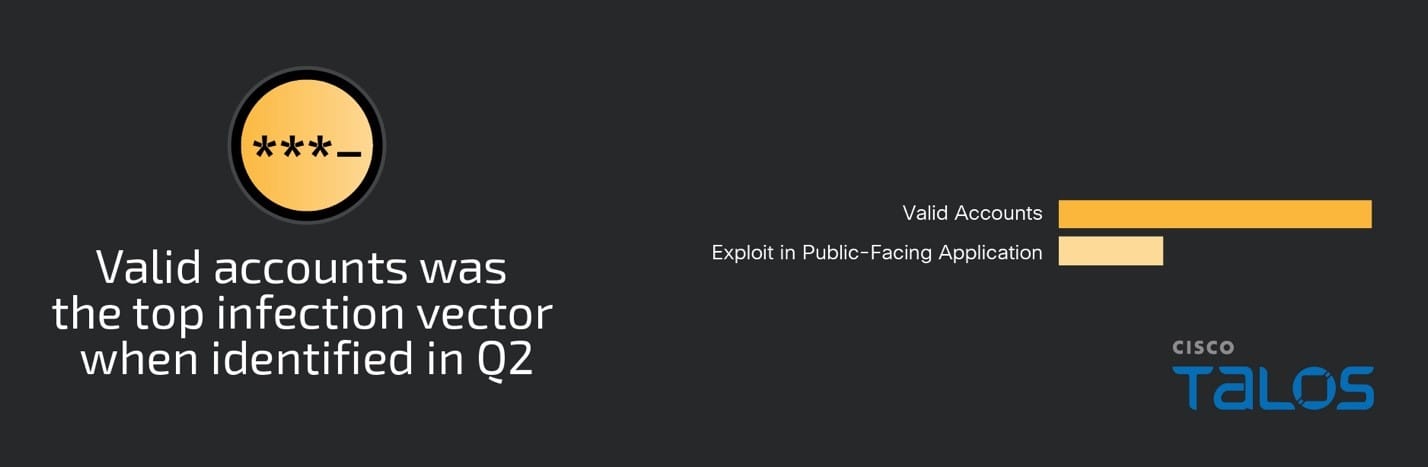
In one engagement this quarter, adversaries compromised an organization’s trusted partner and abused the one-way trust network relationship to gain access. Organizations regularly set up one-way trust network relationships with partners or customers to facilitate controlled access to resources or services, which allows organizations to grant specific permissions or access controls to external entities without reciprocating access.
Although it is intended to enhance security by limiting the potential exposure of critical assets, adversaries commonly abuse this relationship to gain access. As more organizations seek to expand their networks to include more partners and external services, adversaries will likely continue to exploit vulnerabilities within these relationships. Strengthening security controls and continuously monitoring access points will be crucial to mitigating these threats and safeguarding against potential breaches.
Security weaknesses
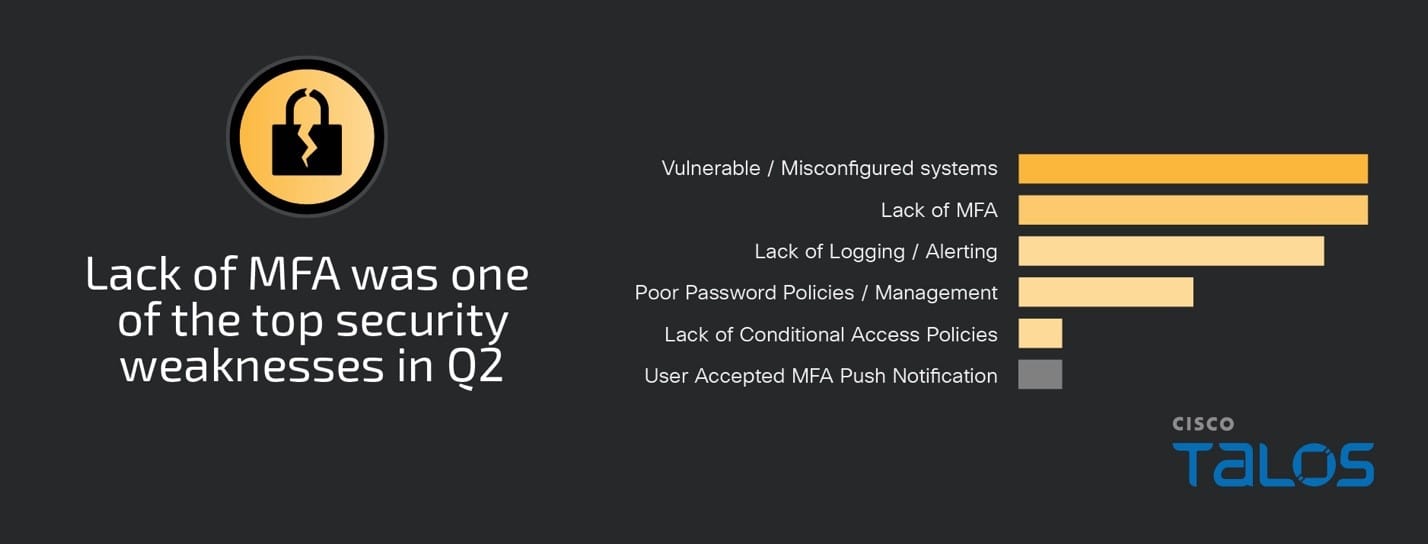
Vulnerable or misconfigured systems and a lack of proper MFA implementation were tied for the top observed security weaknesses this quarter, accounting for nearly all of the engagements. Talos IR observed a 46 percent increase in each of these security weaknesses from the previous quarter.
Systems that are not up to date with the latest patches are potentially susceptible to vulnerabilities. Misconfigured systems are not configured with industry best practices for security in mind leaving the organization exposed, such as a public-facing server that is only supposed to be accessed internally.
In one cluster of activity, a network switch was compromised that was past the device’s EOL support. Using a network switch that is past its EOL support is risky because it no longer receives security updates, bug fixes, or technical support from the manufacturer. Relying on outdated hardware increases the likelihood of unexpected failures and cyberattacks, which can disrupt business operations and result in costly downtime.
In another engagement, the adversaries dumped credentials from the Security Account Manager (SAM) database through the Windows Registry, which enabled the adversary to move laterally throughout the environment because MFA was not properly implemented. There was not enough visibility in the engagement to identify the initial access vector, but organizations must understand MFA can prevent both initial access and lateral movement should an adversary compromise an account or system.
Talos IR recommends implementing MFA on all critical services including all remote access and identity access management (IAM) services. MFA will be the most effective method for the prevention of remote-based compromises. MFA can also help prevent lateral movement by requiring all administrative users to provide a second form of authentication. Organizations can set up alerting for single-factor authentication to quickly identify potential gaps.
This quarter, Talos IR continued to observe users accepting MFA push notifications within engagements, but there was a notable decrease from the large surge in activity seen last quarter. In one cluster of BEC activity, several employees received phishing emails from a trusted partner’s email that had been compromised by the adversary.
The emails contained links to fake login pages meant to harvest credentials. At least one employee provided credentials, which resulted in an MFA push notification being sent to the employee’s phone which they accepted granting the adversary access. Talos IR recommends organizations educate their employees about the specific channels and points of contact for reporting these incidents. Additionally, the employee’s account did not have alerting in place to prevent impossible travel scenarios. Impossible travel refers to the scenario in which a user authenticates from two locations within an unrealistically brief period to have traveled between the locations.
Talos IR recommends reviewing the configurations on identity access management (IAM) platforms for identifying risky login attempts, such as impossible travel to prevent unauthorized access. In addition, organizations should set up monitoring for device registrations and the generation of bypass codes.
Top observed MITRE ATT&CK techniques
The table below represents the MITRE ATT&CK techniques observed in this quarter’s IR engagements and includes relevant examples. Given that some techniques can fall under multiple tactics, we grouped them under the most relevant tactic based on the way they were leveraged. Please note, this is not an exhaustive list.
Key findings from the MITRE ATT&CK framework include:
- PowerShell was the top execution technique observed this quarter, accounting for 41 percent of engagements this quarter, a 33 percent increase from the previous quarter.
- Adversaries created new accounts more than any other persistence technique this quarter, accounting for 18 percent of engagements, more than double what was observed the previous quarter.
- The abuse of remote services, such as RDP, SSH, SMB and WinRM, were observed within 53 percent of engagements this quarter, a slight decrease from the previous quarter.
- The abuse of the LoLBin rundll32 was one of the top defense evasion techniques, accounting for 18 percent of engagements this quarter.
- Talos IR observed a 40 percent increase in remote access software usage this quarter, with AnyDesk being the most observed software, accounting for almost 30 percent of engagements.
Reconnaissance | Example |
T1589.001 Gather Victim Identity Information: Credentials | Adversaries may gather credentials that can be used during their attack. |
T1598.003 Phishing for Information: Spearphishing Link | Adversaries may send a spearphishing email with a link to a credential harvesting page to collect credentials for their attack. |
T1589.003 Gather Victim Identity Information: Employee Names | Adversaries may perform reconnaissance online to try to identify the names of employees to potentially target an organization. |
T1595.002 Active Scanning: Vulnerability Scanning | Adversaries may run vulnerability scans against an organization’s public-facing infrastructure to identify potential vulnerabilities to exploit. |
Resource Development | Example |
T1588.006 Obtain Capabilities: Vulnerabilities | Adversaries may research information about specific vulnerabilities so they can be used within their attacks. |
T1588.005 Obtain Capabilities: Exploits | Adversaries may obtain exploits to vulnerabilities so they can be leveraged within attacks. |
T1584.001 Compromise Infrastructure: Domains | Adversaries may compromise domains so they can use them for malicious activities. |
Initial Access | Example |
T1078 Valid Accounts | Adversaries may use compromised credentials to access valid accounts during their attack. |
T1566 Exploit in Public-Facing Application | Adversaries may exploit a vulnerability to gain access to a target system. |
Execution | Example |
T1059.001 Command and Scripting Interpreter: PowerShell | Adversaries may abuse PowerShell to execute commands or scripts throughout their attack. |
T1059.003 Command and Scripting Interpreter: Windows Command Shell | Adversaries may abuse Windows Command Shell to execute commands or scripts throughout their attack. |
T1047 Windows Management Instrumentation | Adversaries may use Windows Management Instrumentation (WMI) to execute malicious commands during the attack. |
Persistence | Example |
T1136 Create Account | Adversaries may create a new account to maintain persistence in a target environment. |
T1078 Valid Accounts | Adversaries may abuse their access to valid accounts to maintain persistence in a target environment. |
Privilege Escalation | Example |
T1078.002 Valid Accounts: Domain Accounts | Adversaries may abuse their access to valid accounts to maintain persistence in a target environment. |
Defense Evasion | Example |
T1562.001 Impair Defenses: Disable or Modify Tools | Adversaries may disable or uninstall security tools to evade detection. |
T1218.011 System Signed Binary Proxy Execution: Rundll32 | Adversaries may abuse the Windows utility rundll32.exe to execute malware. |
T1027.010 Obfuscated Files or Information: Command Obfuscation | Adversaries may obfuscate commands to evade detection during their attack. |
T1564.008 Hide Artifacts: Email Hiding Rules | Adversaries may create inbox rules to forward certain incoming emails to a folder to hide them from the inbox owner. |
Credential Access | Example |
T1110.003 Brute Force: Password Spraying | Adversaries use a list of usernames and passwords to try and gain access to user accounts. |
T1003.003 OS Credential Dumping: NTDS | Adversaries may dump the contents of the NTDS.dit file to access credentials that can be used for lateral movement. |
T1003 OS Credential Dumping | Adversaries may dump credentials from various sources to enable lateral movement. |
T1110 Brute Force | Adversaries may use brute force account passwords to compromise accounts. |
T1621 Multi-Factor Authentication Request Generation | Adversaries may generate MFA push notifications causing an MFA exhaustion attack. |
Discovery | Example |
T1018 Remote System Discovery | Adversaries may attempt to discover information about remote systems with commands, such as “net view”. |
T1016.001 System Network Configuration Discovery: Internet Connection Discovery | Adversaries may ping a domain to check if the infected device is connected to the Internet. |
T1033 System Owner / User Discovery | Adversaries may attempt to discover information about the logged in user of a compromised account with commands, such as “whoami”. |
Lateral Movement | Example |
T1021.001 Remote Services: Remote Desktop Protocol | Adversaries may abuse valid accounts using RDP to move laterally in a target environment. |
T1021.002 Remote Services: SMB / Windows Admin Shares | Adversaries may abuse valid accounts using SMB to move laterally in a target environment. |
T1021.004 Remote Services: SSH | Adversaries may abuse valid accounts using SSH to move laterally in a target environment. |
T1021.006 Remote Services: WinRM | Adversaries may abuse valid accounts using WinRM to move laterally in a target environment. |
T1534 Internal Spearphishing | Adversaries may abuse a compromised email account to send internal spearphishing emails to move laterally. |
Collection | Example |
T1005 Data from Local System | Adversaries may collect information from an infected system |
T1560 Archive Collected Data | Adversaries may archive staged data using tools, such as WinRAR. |
Command and Control | Example |
T1219 Remote Access Software | Adversaries may abuse remote access software, such as AnyDesk, to establish an interactive C2 channel during their attack. |
T1105 Ingress Tool Transfer | Adversaries may transfer tools from an external system to a compromised system. |
T1071.001 Application Layer Protocol: Web Protocols | Adversaries abuse web protocols, such as HTTPS, for C2 communication. |
Exfiltration | Example |
T1048.003 Exfiltration Over Alternative Protocol: Exfiltration Over Unencrypted Non-C2 Protocol | Adversaries may exfiltrate data over an unencrypted network protocol. |
Impact | Example |
T1486 Data Encrypted for Impact | Adversaries may use ransomware to encrypt data on a target system. |
T1490 Inhibit System Recovery | Adversaries may disable system recovery features, such as volume shadow copies. |